Unblocking WordPress REST API Access
Staq automatically restricts public access to sensitive REST API endpoints — particularly the /wp-json/wp/v2/users/ endpoint.
Since this endpoint is blocked automatically out of the box, it prevents bots or unauthenticated users to enumerate the list of all WordPress users on a site.
This is part of our commitment to hardening your WordPress sites by default, reducing attack surfaces without requiring any manual setup.
What Does This Do?
By default, any unauthenticated request to /wp-json/wp/v2/users/ will now return the following error response:
{
"code": "rest_user_cannot_view",
"message": "You are not allowed to access this endpoint.",
"data": {
"status": 401
}
}
This prevents bots and scrapers from querying your site to discover usernames — a common first step in brute-force or credential stuffing attacks.
How to enable the user’s endpoint?
If your application or a certain plugin requires access to this endpoint, it’s very easy to enable.
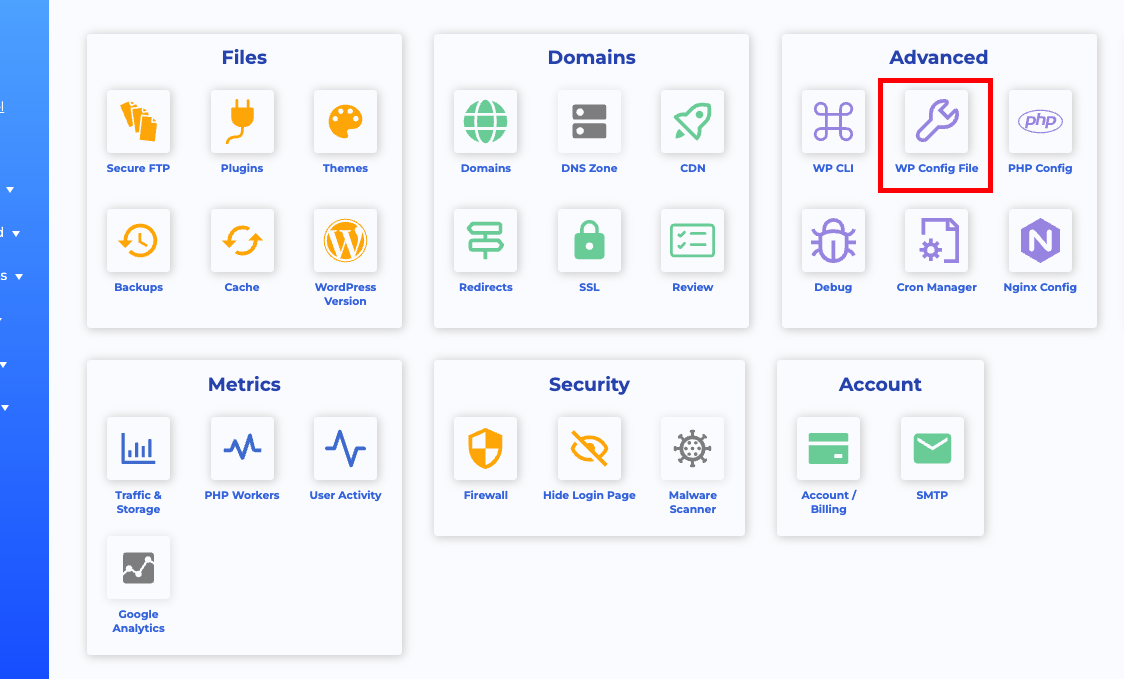
To do so, define the following constant in the site’s by going to the site’s Staq Panel, followed by clicking WP Config File:
Click Add and enter:
ELM_BYPASS_REST_API_PROTECTION as the Name and true as the Value:
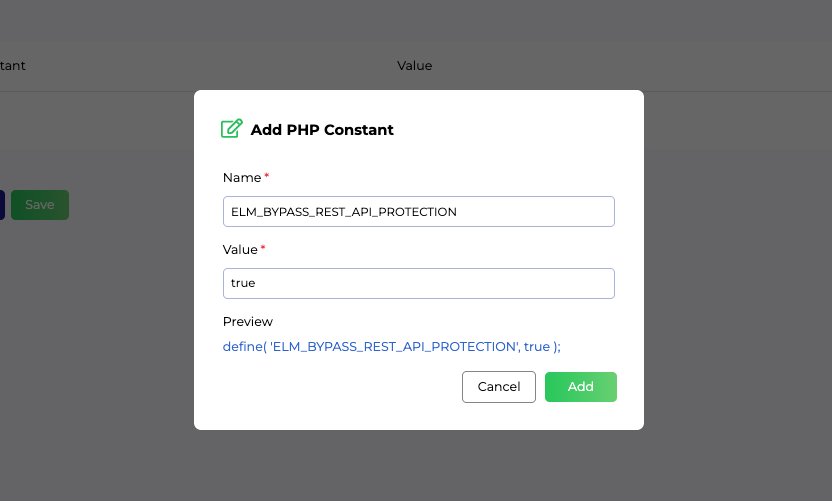
Click Add and make sure you also click Save.
Important: You cannot modify the wp-config.php file via SFTP, as our system will override it for security reasons. Instead, please follow our official guide to edit your config file safely inside the Staq dashboard: How to edit the wp-config.php file on Staq
Why This Matters — The Benefits
- Improved Security: Blocks REST API user enumeration attacks — a known vector for brute-force and phishing attacks.
- Less Bot Traffic: Prevents bots from crawling user information that could be used maliciously.
- No Plugin Required: This is enabled automatically for every Staq-hosted site — no additional configuration or third-party plugins needed.
Conclusion
This feature strengthens your website’s default security posture without sacrificing developer flexibility. By protecting critical REST API endpoints by default — and offering a simple opt-out — you get the best of both worlds: robust security with total control.
Need some help?
We all do sometimes. Please reach out to our support team by dropping us a support ticket. We will respond fast.